Mobile Phone Security
Mobile technology has come to play a major role in society. In countries all over the world, smart phones, tablets, and other such mobile devices are winning over the hearts of consumers. These devices have made it easier for people to stay connected to one another and ensure that they have constant access to the Internet and various other resources. It could be suggested that mobile technology has revolutionized humanity, but technological progress often comes at a cost.
The advent of mobile technology also brought more exposure to the threat of hacking and other forms of cybercrime.
Because so many people rely on their mobile devices in their daily lives, the security of these devices has become a serious issue, especially amongst the various telecommunications and mobile network operators that have invested in them. Mobile security is a major aspect of mobile computing that encompasses the myriad protection techniques that are used to keep smart phones and other devices safe.
Shortfalls in mobile security can mean the theft of personal information. 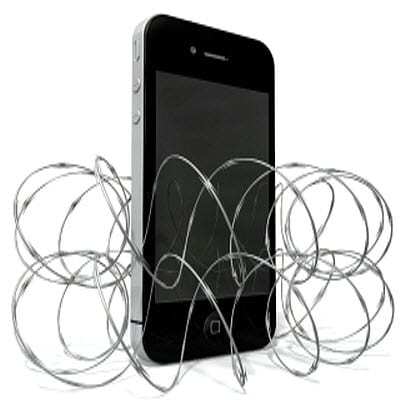
This information is valuable to hackers because it could be used to access credit cards, bank accounts, and could easily lead to more intricate forms of identity theft. If a mobile device is not secure, it could essentially be turned into another tool for a hacker and could be used to infect other devices. The threats facing mobile devices are constantly evolving and adapting to the security measures that are established to mitigate the damage they may cause.
Because of the ever-changing nature of hackers, mobile security takes a wide variety of forms.
Security software, such as antivirus and firewall suites are available for some smart phones, allowing users to catch malicious and stop attacks before they cause too much harm to a mobile device. Some malicious programs are able to bypass these security methods, but can still be caught because of the resources they use to operate. Resource Monitoring systems track the resources of a mobile computing system. Some malicious program access certain resources, a telltale sign of their intent. A Resource Monitoring system can lock these resources when they are access in a peculiar fashion, rendering malicious programs ineffective.
There are a vast multitude of mobile security measures that can be taken to ensure the safety of a smart phone or tablet, but none of these methods will be guaranteed to work for the entirety of a smart phone’s lifespan. This is due to the evolving nature of cybercrime and the fast pace at which technology, both malicious and otherwise, advances. What may make a mobile device secure one day, may actually be the reason it is vulnerable the next. Because of this, there is not mobile security measure that can be taken that will make a device impossible to exploit.
